Get the top crypto news stories weekly, right here, with Crypto Espresso.

How to Secure Cryptocurrency and Protect Your Digital Assets
February 26, 2023

How to Secure Cryptocurrency and Protect Your Digital Assets
February 26, 2023
How to Store and Secure Cryptocurrency
One of the biggest benefits of cryptocurrency is also one of its slippery banana peels – when it comes to crypto storage, the buck stops with you. This means you need to take extra care when deciding how to store and secure cryptocurrency safely, which isn’t as simple as buying a nice leather wallet and popping them in there for safekeeping.
For this reason, it is important you have a crypto security checklist. There are many different ways to store cryptocurrency – each with varying pros and cons. So, in this article, we’ll examine the various ways you can store your coins so you can work out which is the best cryptocurrency storage method for you, and avoid cryptocurrency security issues.
Let’s Talk About Secure Cryptocurrency
The first thing to know when discussing cryptocurrency storage is to know what exactly you are storing. To understand this, we can compare a blockchain to a railway network. Imagine the trains on the network being the coins themselves, constantly moving around it.

All coins share the same network and must remain on it at all times. This means you can’t simply lift your coins off the rails and hide them somewhere or store cryptocurrency in your sock drawer.
Since you can’t physically remove your coins from the tracks, you need a secure place where you can lock them away until you need them. Of course, you’ll also need to know what and what not to do when using a crypto exchange.
When creating a cryptocurrency wallet of any kind, you are given a ‘digital address’ for each blockchain you want to use (e.g. Bitcoin, Ethereum, XRP). These addresses act as the depot on the network, keeping your coins in a separate track away from the main line.
So, if the address is where your coins are kept, what does the wallet do? The wallet protects the addresses from intruders, preventing cryptocurrency security issues or someone else from accessing the depot and removing the coins.
It also allows the legitimate owner to move their coins in and out, or interact with various crypto platforms, with different wallet types offering different levels of security and practicality to secure cryptocurrency safely.
With that understood, let’s get into the key aspects of cryptocurrency storage for the next point in this crypto security checklist.
Public Keys vs Private Keys
When you create a new crypto wallet to store cryptocurrency, there will be a few things to note down during the setup process. One of these will be the various public keys, while another will be the single private key. This is very important to prevent cryptocurrency security issues.
The public key is simply the address for each coin you want to add, so you won’t need to record this, but the private key is another thing entirely. The private key is the master password to your entire wallet, which is about as important as it sounds. Anyone who has your private key can import it into their own wallet and simply ship your coins out.
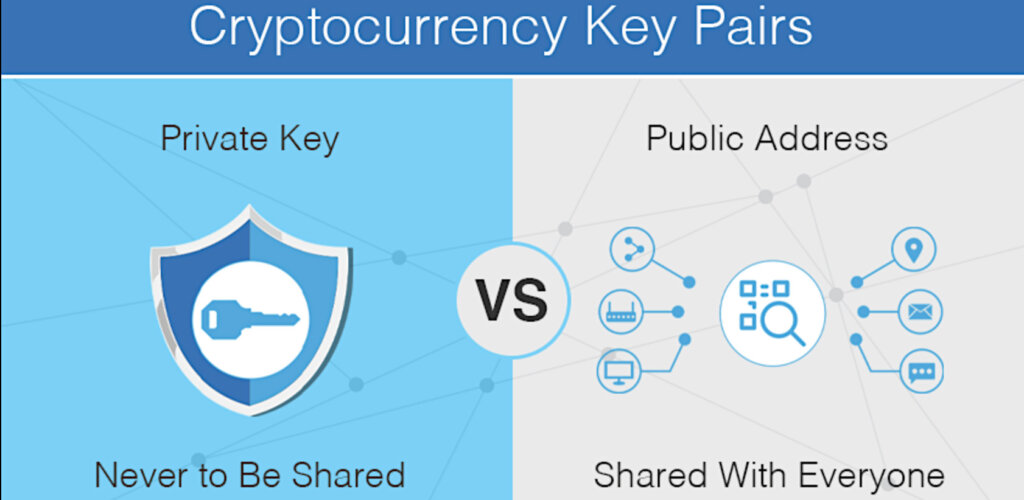
It’s for this reason that you should be 100% clear on who holds the private key to your wallet when you create one, which we’ll cover next.
Custodial vs Non-Custodial Wallets
When we talk about ‘custody’ in this manner, we’re not talking about custody of your coins, but rather of your private key. Custodial wallets are those that you typically find in an app store, including all secure cryptocurrency exchange apps, and are wallets over which you have limited or no control when you store cryptocurrency in these wallets.
The private key is stored on a server belonging to the company running the service, which means you must put your faith (and funds) in the security of the company in question. You will also have to hand over personal information to comply with local regulations when setting the wallet up.
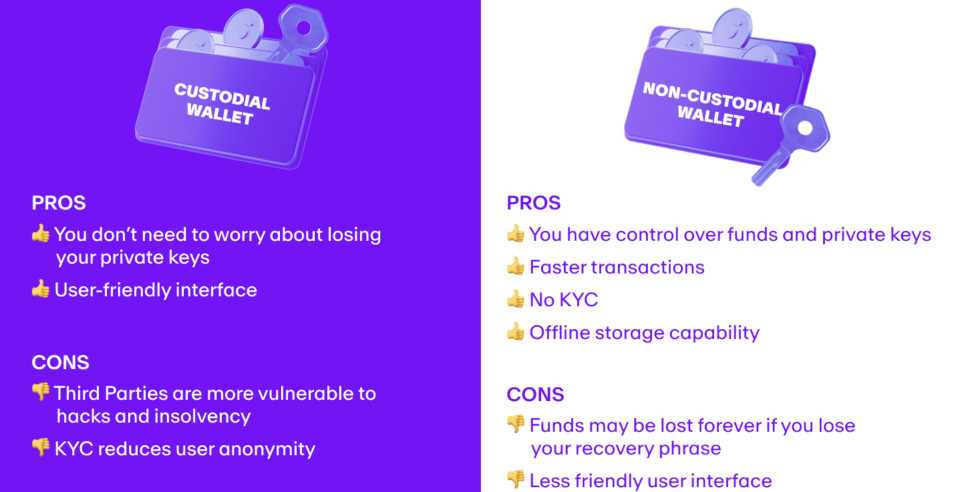
Non-custodial wallets on the other hand are those that allow you to retain the private key, putting you in full control of your funds. Many non-custodial wallets will not require you to hand over personal information during setup, another reason why they are favored by the cryptocurrency community, which is something to consider for your crypto security checklist.
Hot Wallets vs Cold Wallets
Something else to factor into your decision-making when it comes to cryptocurrency storage is whether you want a hot wallet (software wallet) or a cold wallet (hardware wallet). This essentially refers to whether the wallet is connected to the internet or not, which can impact how you store cryptocurrency, and how secure cryptocurrency really is.
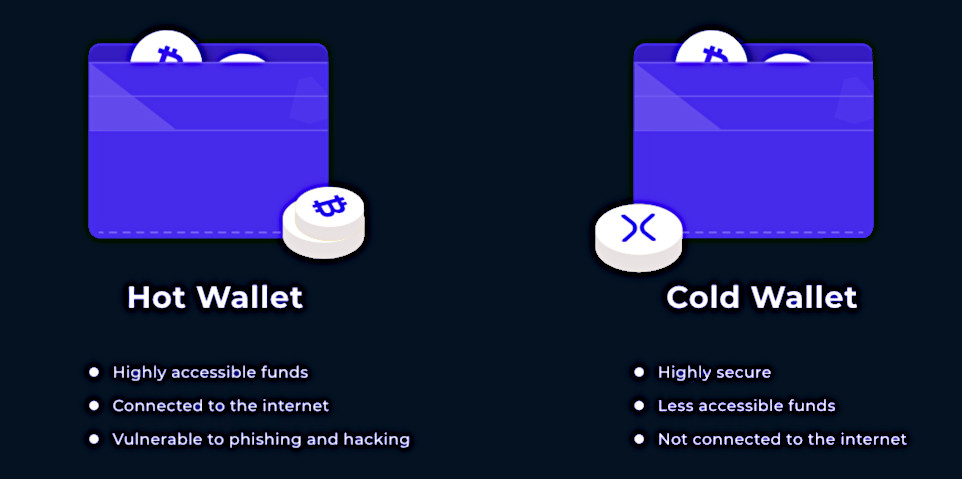
As you would expect, wallets kept on mobile devices and computers are considered to be hot wallets because they are almost always connected to the internet when the device is turned on.
This goes for all custodial wallets too. These are connected to the internet through the servers of the operator at all times. Hot wallets are usually used by people who want quick and easy access to their cryptocurrencies, for example, if they want to spend them in a shop or gamble with bitcoin online.
But hot wallets usually come with more security concerns – anything connected to the internet is at risk of being compromised. This means that these wallets are only as secure as the device on which they are installed.
Cold wallets, on the other hand, are wallets that are kept offline at all times. This makes them ideal for a long-term means to secure cryptocurrency. However, they are not the most convenient way to store cryptocurrency if you want to access your funds instantly.
Different Types of Cryptocurrency Wallet
Now we know the key terminology, let’s take a look at the different types of cryptocurrency wallets out there, and who they are suitable for.
Mobile Wallet
As we’ve already discussed, mobile wallets come in the form of apps and are usually custodial, although non-custodial mobile wallets are out there, and all are considered hot wallets. Here is a look at the Coinbase custodial mobile wallet.
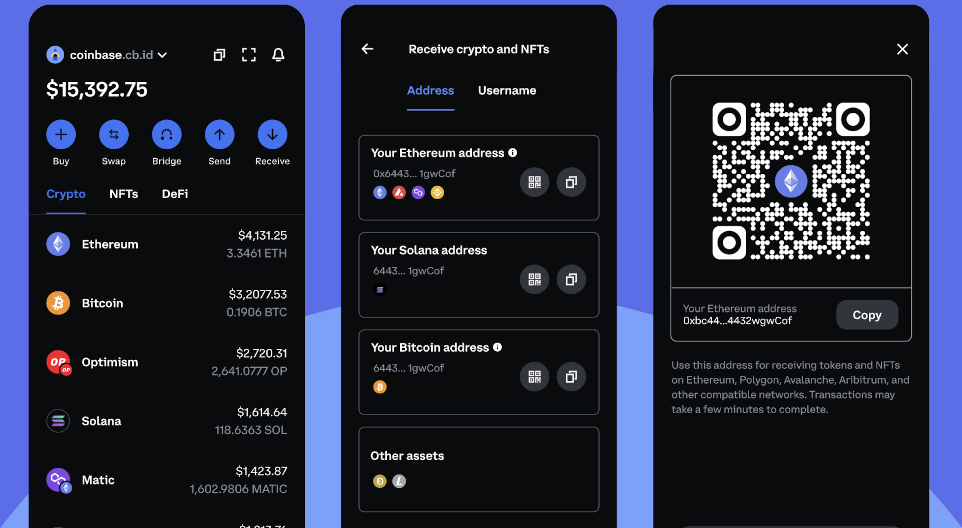
Mobile wallets are great for keeping small amounts of cryptocurrency as a backup form of payment. They’re also perfect for crypto gambling and other forms of online entertainment as you can seamlessly make deposits and withdrawals on mobile-friendly sites. Even though the technology has improved to make them more secure than ever, they are not suitable to store cryptocurrency in large amounts.
Desktop Wallet
Similar to a mobile wallet, desktop wallets are considered hot wallets, although there is a bigger choice of non-custodial desktop wallets to choose from to secure cryptocurrency.
These include the core client of a blockchain (for example the Bitcoin Core client), which allows the computer in question to act as a node, helping to confirm transactions and secure the network as well as send, receive, and store coins.
As with mobile wallets, a desktop wallet is only as secure as the device on which it is installed and should not be considered suitable for high-value or long-term storage – an important point for your crypto security checklist.
Decentralized Web Wallet
A decentralized web wallet is a hot wallet that allows the user to engage with the Web 3.0 world while storing cryptocurrencies and digital assets. These wallets are typically non-custodial and can be accessed through a browser plugin or mobile app, which puts the onus on the user to download the correct software in each instance.
Decentralized web wallets have become extremely popular with the growth of Web 3.0 and are much safer and help to prevent cryptocurrency security issues far better than the original type of web wallet, which is now largely defunct.
Hardware Wallet
A hardware wallet is the safest way of storing cryptocurrencies that exists today. Rather than being wallets themselves, these are physical devices that are needed to confirm every single cryptocurrency transaction the user wants to make.

The wallet part is typically a non-custodial mobile app that acts as the front end, with the hardware device used to confirm any transaction requested by the wallet. Put simply, no one can get funds out of the mobile wallet without confirming it on the hardware wallet first. Think of it as dedicated two-factor authentication for your crypto wallet to store cryptocurrency safely.
Hardware wallets are stored offline – ideally in a secure environment, such as a home safe (not your sock drawer) when not being used. This means they cannot be remotely compromised. Some are also ‘air gapped’, meaning they simply don’t have the functionality to connect to the internet in the first place.
Which Crypto Wallet Is the Best?
There’s no simple answer to the question of which crypto wallet is best to secure cryptocurrency, because all wallets fulfill different functions. The ideal solution is to have the bulk of your cryptocurrency protected by a hardware wallet, and have a small amount on a mobile app for trading or spending.
This way, you have the practicality and flexibility of the mobile app and the long-term security of offline storage.
Oh, and never, ever, give your private key out to anyone. ?
Rebecca Chalmers